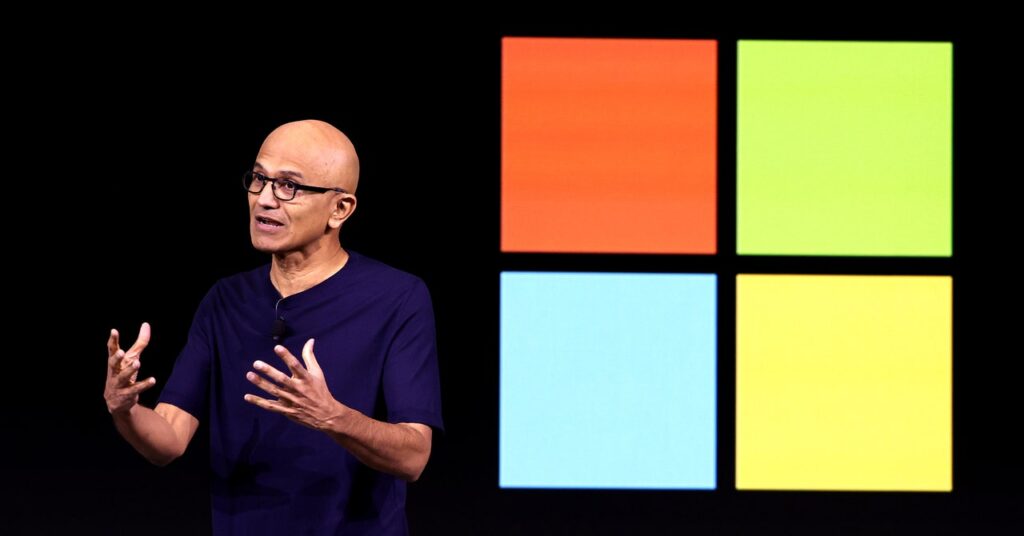
Microsoft’s CEO Satya Nadella has hailed the corporate’s new Recall characteristic, which shops a historical past of your laptop desktop and makes it out there to AI for evaluation, as “photographic reminiscence” to your PC. Inside the cybersecurity neighborhood, in the meantime, the notion of a instrument that silently takes a screenshot of your desktop each 5 seconds has been hailed as a hacker’s dream come true and the worst product concept in current reminiscence.
Now, safety researchers have identified that even the one remaining safety safeguard meant to guard that characteristic from exploitation may be trivially defeated.
Since Recall was first introduced final month, the cybersecurity world has identified that if a hacker can set up malicious software program to achieve a foothold on a goal machine with the characteristic enabled, they’ll shortly acquire entry to the person’s whole historical past saved by the perform. The one barrier, it appeared, to that high-resolution view of a sufferer’s whole life on the keyboard was that accessing Recall’s information required administrator privileges on a person’s machine. That meant malware with out that higher-level privilege would set off a permission pop-up, permitting customers to forestall entry, and that malware would additionally probably be blocked by default from accessing the info on most company machines.
Then on Wednesday, James Forshaw, a researcher with Google’s Venture Zero vulnerability analysis staff, revealed an replace to a weblog put up declaring that he had discovered strategies for accessing Recall information with out administrator privileges—primarily stripping away even that final fig leaf of safety. “No admin required ;-)” the put up concluded.
“Rattling,” Forshaw added on Mastodon. “I actually thought the Recall database safety would at the very least be, , safe.”
Forshaw’s weblog put up described two completely different methods to bypass the administrator privilege requirement, each of which exploit methods of defeating a fundamental safety perform in Home windows generally known as entry management lists that decide which parts on a pc require which privileges to learn and alter. One in every of Forshaw’s strategies exploits an exception to these management lists, briefly impersonating a program on Home windows machines referred to as AIXHost.exe that may entry even restricted databases. One other is even less complicated: Forshaw factors out that as a result of the Recall information saved on a machine is taken into account to belong to the person, a hacker with the identical privileges because the person may merely rewrite the entry management lists on a goal machine to grant themselves entry to the complete database.
That second, less complicated bypass approach “is simply mindblowing, to be trustworthy,” says Alex Hagenah, a cybersecurity strategist and moral hacker. Hagenah not too long ago constructed a proof-of-concept hacker instrument referred to as TotalRecall designed to indicate that somebody who gained entry to a sufferer’s machine with Recall may instantly siphon out all of the person’s historical past recorded by the characteristic. Hagenah’s instrument, nonetheless, nonetheless required that hackers discover one other method to acquire administrator privileges via a so-called “privilege escalation” approach earlier than his instrument would work.
With Forshaw’s approach, “you don’t want any privilege escalation, no pop-up, nothing,” says Hagenah. “This could make sense to implement within the instrument for a foul man.”